
Accounting Outsourcing Security Checklist for CPA Firms 2026

When you outsource accounting work, you are not just solving for capacity. You are choosing where your clients’ most sensitive financial data will live, who can see it, and what safeguards stand between it and potential threats.
This is not just another operational or strategic call; it is a decision that defines your firm’s security posture.
Data from Verizon’s Data Breach Investigations Report shows that financial and professional services firms remain among the most targeted sectors for cyberattacks. For CPA firms, the impact is not just financial. It is reputational and regulatory.
The stakes are real.
Sensitive data includes client tax returns, payroll records, bank details, and financial statements. If you do not give this data the vigilance it deserves, you risk opening the door to fraud, regulatory penalties, and lasting reputational harm.
This also means that your responsibility to protect that data does not change when the work moves outside your firm. The AICPA is clear on this. It states, “Outsourcing does not transfer responsibility. CPA firms remain accountable for safeguarding client data, regardless of where the work is performed”.
This is why leading firms are not asking, “Should we outsource?”
They are asking, “How can we outsource securely?”
A well-defined accounting outsourcing security checklist is how you answer that.
Before the Checklist: Understand Your Data Flow
Most firms jump straight into certifications and controls. That is the obvious thing to do, but also the wrong way to start. Security should begin with this one simple question:
How does your data actually move? This question further breaks down into?
- Where is client data stored while work is being done?
- How does the outsourcing team access your systems?
- How is completed work shared back?
Take note of all the answers you get. If anything involves email attachments, shared drives, or ad hoc access, you already have a problem.
There are some industry best practices that, when followed, ensure there is no breach and that the data remains safe. These practices include:
- Data should sit in secure cloud systems or portals.
- Access should be controlled, logged, and authenticated.
- File transfer should never rely on email.
Only after you map this flow does a checklist become meaningful.

The Accounting Outsourcing Security Checklist
This checklist reflects how leading CPA firms evaluate secure accounting outsourcing partners today.
1. Access Control
It’s commonly assumed that most security breaches in outsourcing are complex, but they are often simple, like failing to follow common guidelines, such as:
Too many people having access, Access not being reviewed or sharing credentials
A secure and robust infrastructure enforces:
- Role-based access (only what is needed)
- Multi-factor authentication
- Immediate revocation when roles change
This is the backbone of accounting data security controls and should be give utmost attention.
2. Controlled Work Environment
One of the biggest gaps in data security in accounting outsourcing is where work happens. Disciplined providers having security maturity do not allow work on personal machines or open networks.
Instead, they use:
- Virtual desktop infrastructure (VDI) or secure environments
- Managed devices with monitoring
- Restricted download and copy controls
This ensures data never leaves a controlled environment and adhering to this is one of the biggest responsibilties a provider has to perform.
3. Encryption and Data Protection Standards
Encryption is often misunderstood as a technical detail. Whereas, it should be treated as a fallback protection. In true terms, data should be:
- Encrypted at rest (stored data)
- Encrypted in transit (when shared or accessed)
The encryption process ensures that even in worst-case scenarios, data remains unusable. This is central to financial data protection in outsourcing.
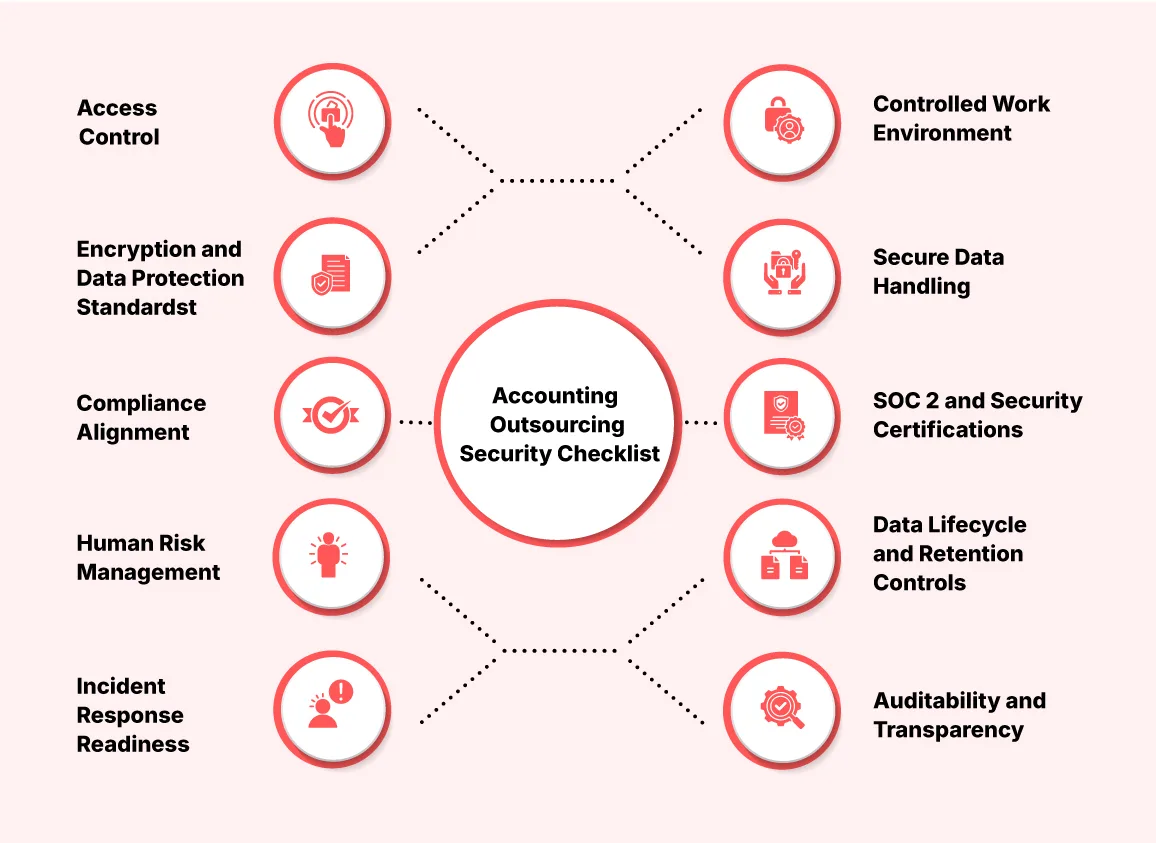
4. Secure Data Handling
Many risks come from “small” habits, such as downloading files locally, sending documents over email or storing backups in multiple places. Techinally strong providers eliminate these behaviors through various proactive security measures. Some of the most common ones are:
- Secure portals
- Controlled file transfer systems
- Activity logging
5. Compliance Alignment Is Non-Negotiable
Your outsourcing partner must operate within the same regulatory expectations as your firm. They should also effectively create a compliance framework in adherence to:
- Internal Revenue Service (IRS) requirements
- US GAAP
- GDPR (if applicable)
This alignment ensures genuine compliance in accounting outsourcing. Without a compliant infrastructur, your firm remains exposed, even if the work is performed correctly.
6. SOC 2 and Security Certifications
Certifications are not sufficient on their own, but they are strong indicators of security standards. SOC 2 evaluates how well a provider manages security, confidentiality and availability. It also verifies that controls are consistently applied, not merely documented.
For CPA firms, SOC 2 serves as a reliable benchmark for security best practices in accounting outsourcing.
7. Human Risk Management
Human errors are inevitable. and sometimes these human errors play a crucial role in data breaches. Common human risks include- Lack of awareness, Poor handling practice and Insider threats.
A strong and proactive mitigation framework ensures minimal damage. These measures include
- Background checks
- Structured training
- Clear accountability
8. Data Lifecycle and Retention Controls
The risk associated with data increases over time. Storing data longer than necessary, or across multiple systems, increases the risk of exposure.
Strong partners define:
- Where data is stored
- How long is it retained
- How is it securely deleted
Data lifecycle and retention controls are fundamental to accounting outsourcing risk management.
9. Incident Response Readiness
No system is completely immune to failure. But the effectiveness of response, in both speed and clarity, is critical. The provider should have these non-negotiables:
- A tested incident response plan
- Defined notification timelines
- Clear escalation protocols
Without a clear response plan, even minor incidents can escalate into major issues.
10. Auditability and Transparency
Trust is established through evidence, not claims. You should be able to:
- Review audit reports
- Validate controls
- Request security documentation
Providers who lack transparency create significant blind spots.
Also Read: IRS Compliance in U.S. Accounting Outsourcing: 2026 Guide
Where Most CPA Firms Get This Wrong?
If you’re thinking that outsourcing is where the mistake begins, you are probably wrong. Outsourcing is now a mandate. Forward looking firms are going all in on offshoring tasks.
Then, what is the real mistake, and how can you avoid it?
The mistake is treating security as a checklist instead of a system.
Firms often focus on certifications and not actual workflows. They overlook data movement and handling, assuming that the responsibility transfers to the vendor.
Well, reality check: It does not.
Research and industry experience consistently show that outsourcing risk is not about geography; it is about control and oversight. Strong governance and structured controls can significantly reduce both performance and security risks.
Security Is What Makes Outsourcing Sustainable
Outsourcing works when three things align: Capacity, Quality, and Control.
You’re probably wondering why security isn’t a part of the pillar. This is because ‘Security sits inside Control’.
A robust accounting outsourcing security checklist is not just about avoiding risk. It is what allows you to scale confidently, take on more clients, and expand services without hesitation. This is also where the choice of partner becomes critical.

Firms like QX Accounting Services are increasingly being recognized not just for their delivery capabilities but also for how well they integrate secure accounting outsourcing, compliance alignment, and operational transparency into their model.
From SOC 2-aligned processes to teams trained in U.S. regulatory frameworks, the main concern about outsourcing is shifting from “Can they do the work?” to “Can they do it in a way that stands up to audit, scrutiny, and scale?”
Because in the end, outsourcing is not just about efficiReady to Evaluate Your Current Setup? ency. It is about trust that holds under pressure.
If you are already outsourcing or planning to, you need clarity on one thing:
Is your current model truly secure, or just operationally efficient?

Ready to Evaluate Your Current Setup?
Start with a structured review. Let us have a conversation.
Click Here!FAQs
What are the common security risks in accounting outsourcing?
Most risks in accounting outsourcing are neither complex nor technical. They are basic, simple risks that usually stem from weak controls, unclear processes, or poor oversight.
Some of the most common risks include:
- Excessive or unmanaged access to client data
- Use of unsecured devices or networks
- Data sharing through email or informal channels
- Lack of encryption and secure storage
- Weak employee training and accountability
What should CPA firms include in an accounting outsourcing security checklist?
A strong accounting outsourcing security checklist should go beyond any surface-level controls. It should cover the full data lifecycle from access to storage to deletion.
Some of the key points include:
- Access control (role-based access, MFA, no shared credentials)
- Infrastructure security (secure environments, monitored systems)
- Data protection (encryption in transit and at rest)
- Compliance alignment (IRS, US GAAP, GDPR, where applicable)
- Incident response and auditability
The only thing we need to ensure is that data remains protected at every stage, not just at entry points.
How can firms evaluate data security before outsourcing accounting?
Along with evaluating a provider’s certifications, firms should also understand how their own data will move within the outsourced setup.
It’s important to map out a few bits first. Understand
- Where the data will be stored
- How teams will access it
- How it will be shared or transferred
And then go ahead and assess the provider’s controls around:
- Access and authentication
- Encryption standards
- Work environment (secure systems vs local devices)
- Monitoring and audit logs
If these elements are unclear or inconsistent, the outsourcing model is likely to carry avoidable risk.
What security standards should accounting outsourcing providers follow?
Outsourcing providers should align with both regulatory requirements and recognized security frameworks to ensure consistency and accountability.
Key standards include:
- Internal Revenue Service (IRS) requirements for handling taxpayer data
- US GAAP for financial reporting alignment
- GDPR where international data is involved
- SOC 2 for operational and security controls
These standards ensure that outsourcing is not just efficient, but also compliant and defensible.
How can firms verify the compliance and security practices of outsourcing providers?
Verification should always be evidence-based, not assumption-based.
Firms should request and review:
- SOC 2 reports or equivalent certifications
- Documented security policies and procedures
- Access control frameworks and user management processes
- Incident response plans
- Audit logs or reporting samples
In addition, conducting a structured vendor risk assessment before onboarding can help identify gaps early and avoid future issues.
Why is SOC 2 compliance important in accounting outsourcing?
SOC 2 is important because it evaluates how well a provider manages data security over time, rather than at a single point in time.
It focuses on key areas such as: Security, Confidentiality and Availability
For CPA firms, this provides assurance that the provider’s controls are not only in place but also consistently followed, making it a strong benchmark for accounting outsourcing security best practices.
What questions should CPA firms ask about security before outsourcing accounting services?
The right questions help uncover how mature a provider’s security framework really is.
Firms should ask:
- How is client data accessed and controlled?
- Do you use secure environments such as VDI?
- What encryption standards are followed?
- Are you SOC 2 compliant or equivalent?
- What is your incident response process?
- How do you ensure compliance with IRS requirements?
Clear, structured answers indicate strong processes while vague or generic responses often signal gaps.

Bhagyashree Patankar
With over 14 years of global experience in finance and accounting, Bhagyashree is a Chartered Accountant and US CPA with a master’s in Accounting and Finance. She leads an 80+ member team across accounting, audit, and tax, driving operational excellence, talent development, and high-quality delivery. Known for her precision and strategic insight, she transforms financial data into actionable business strategies that enhance decision-making, efficiency, and sustainable growth.
Unauthorized copying or plagiarism of our content is a violation of intellectual property rights. We take such matters seriously and will pursue legal action to protect our original work. Anyone found engaging in such activities will be held accountable under applicable laws.
Our Latest Insights
Let’s Work Together
Explore outsourcing solutions, request a free trial or discuss your practice’s needs with our expert consultants.







 Get Your ROI Estimate
Get Your ROI Estimate 